Now You Can Rescue All Files Corrupted After Virus Attack
- About Computer Virus
- Common Viruses You May Encounter
- How Can Virus Infect Computer and File
- How to Recover Files Corrupted by Virus
Content:
About Computer Virus

The so called computer virus is actually a set of computer instructions or program codes with self-replication function and they are established in or inserted into computer programs to destroy computer functions or ruin data so as to lay impact on computer use. Just like biological virus, computer virus also has a stunning propagation speed. Computer virus can be attached to various types of documents, programs and storage devices. So when we copy an infected file or program to other device or connect a mobile storage device attacked by virus to a clean computer, we help complete a spreading process.
A computer virus is often hidden in the accessible information resources of operating system (OS) and it can make itself duplicating and spreading through making use of such resources. Thus, devastating attacks will be performed to OS while the computer is running. The reasons why computer virus appears can be divided into three types:
1.Mischief: try to seek stimulation by fooling others.
2.Revenge: try to beat others who have conflicts with the virus creators.
3.Making profit: try to get confidential information to earn misbegotten money.
Six obvious characteristics of virus are: reproductive ability, destructiveness, infectiousness, latency, invisibility and triggering ability.
- Reproductive ability: according to what we said before, computer viruses can reproduce like biological viruses. When normal program runs, it also runs to start self-replicating. In fact, whether a program is equipped with the features of reproductive ability and infectiousness or not becomes the primary condition to determine a virus.
- Destructiveness: after a computer has been infected, the normal programs in it may stop running and files in it may be deleted or damaged to some extent. Moreover, the BIOS, boot sector as well as hardware environment may also be destroyed.
- Infectiousness: the infectiousness of computer virus can be reflected in the process when virus spread its copies or variants to other clean programs through modifying. By the way, the target can also be one component in OS.
- Latency: it refers to the ability of computer virus to be parasitic by attaching itself to other media. The invaded virus will not be activated until the conditions are ripe and when it is activated, the computer running speed will become very slow.
- Invisibility: computer virus often has a strong sense of concealment, so we can only find a small number of viruses by using antivirus software. This feature makes it flickering and changeable, so it is very hard to deal with.
- Triggering ability: the virus creators often set some trigger conditions, such as a certain time or date of the system clock and the running of a certain program. Once the conditions are met, the computer virus will be initialized to destroy system.
Common Viruses You May Encounter

It is hard or even impossible to estimate the type and quantity of virus. The update rate and reproduction rate of virus is very stunning. Perhaps, tens of thousands of viruses are invading users’ computer every second. We plan to share some commonly seen viruses here so that users can roughly analyze the risk of virus and take appropriate actions to deal with it.
According to the media where it locates, computer virus can be divided into three types: network virus, file virus and boot virus. The network virus attacks executable files in network; file virus attacks files in computer; boot virus often invades boot sector and system MBR. In addition, there is also mixed virus combined by any two (or all) of the above three types.
Computer virus can also be classified to resident virus and non-resident virus according to its infection method. After resident virus infected a computer, it will leave portion of itself in system memory (RAM) and this part of program will be merged into OS. The resident virus is always active until the computer shuts down or restarts. Well, non-resident virus will be activated when getting a chance, but it will not infect computer memory. Some viruses of this type will also leave small part in the memory, but it’s not their transmission channel.
No dangerous type: this virus only simply reduces the memory, displays images and makes a sound.
Dangerous type: obviously, this kind of virus will cause serious errors in computer system operation.
Very dangerous type: this virus type often removes programs, destroys data and clears the system memory area and important information in OS. Unpredictable and catastrophic damage will be caused if a computer is infected with such virus. Errors will be generated in other programs due to virus infection and this will result in file damage as well as sector damage. And it is a wrong conception that no dangerous virus will always be harmless. In some special cases, it also brings damages to new versions of DOS, Windows and other operating systems.
Companion virus: it doesn’t aim at changing the document itself. Instead, it generates companion files in accordance with EXE files, with the same name but different extensions, by using special algorithm. When DOS loads files, the companion files will be loaded firstly and then it will execute the original EXE files.
 “Worm” virus: this kind of virus spreads through networks without changing documents and other information. By taking advantage of network, it disseminates the virus copies from one computer memory to another. In general, it has no other bad effects in addition to occupying memory. Some worms (such as CodeRed) achieve proliferation and destruction through making use of software bugs.
“Worm” virus: this kind of virus spreads through networks without changing documents and other information. By taking advantage of network, it disseminates the virus copies from one computer memory to another. In general, it has no other bad effects in addition to occupying memory. Some worms (such as CodeRed) achieve proliferation and destruction through making use of software bugs.
Variant virus (also known as the Phantom Virus): this type of virus uses a complex algorithm to make each of their own copy spreading with different content and lengths. It is often made up from decoding algorithms mixed with unrelated instructions and variant virus.
Macro virus: it is designed for specific applications. It can be attached to the macro instructions in some applications and is able to spread through email attachment, floppy disk, file download, group software, etc. Written in easy programming language, such as VisualBasic and CorelDraw, macro virus becomes the most popular virus since it had been discovered in 1995.
Trojan: this virus seems to be very normal, but it will conduct some vicious and wrongful activities when executed. It is frequently used as a tool for hackers to steal users’ password information and destroy data or programs in hard disk. Trojan does not replicate itself, on the contrary, it induces computer users to install the programs or download files infected with it.
How Can Virus Infect Computer and File
Sometimes, you may find all files corrupted after virus attack (either all files in a partition or a whole hard disk), but you often don’t even have a clue on how does that happen. The natural reaction of most users is to try to figure out answers to the question – how to recover files corrupted by virus. Now, please allow us to analyze the invading methods of virus. Those methods can be basically divided into three types:1.Computer hardware: although only a few viruses are spreading through unmovable computer hardware like dedicated ASIC chips and hard drives, they have a strong sense of destructiveness. And up to now, there is no proper testing method or solution.
2.Mobile storage device: with the fast development and maturity of mobile storage device, it becomes a good medium for virus to survive. When you connect your storage product, such as USB flash drive and memory card, to computer for data exchanging, you may get your mobile device attacked if the computer has fallen victim to virus. Or if your movable storage device is infected by virus, you will make it spread to computer in such process.
3.Network: as network becomes more and more indispensable among our life, the frequency of storage device getting attacked by virus is growing. When you download documents, pictures or movies from internet, you are easy to get infected.
After reading those methods, you may realize it’s better to prevent device being attacked by virus as much as possible than trying to recover all files corrupted after virus attack. Image that you find your important files stored in computer or other devices are destroyed by virus, how depressed will you be? We guess you may be freaked out, losing your mind and having no idea of how to overcome this difficulty.
So please keep those things in mind: don’t download data with unknown pathway from internet; make sure only your trustworthy friends or family members can use your mobile storage device. Just remember to be very cautious when you exchange data with network or between different devices.
All in all, knowing above invading methods of virus and virus preventing suggestions could be very helpful if you don’t want to accomplish virus corrupted files recovery after disaster occurs.
How to Recover Files Corrupted by Virus
If your computer is under attack and you discover file corruption now, you need to try your best to minimize the losses that would be brought by such attack. But please don’t try to kill the virus first by using antivirus tools.Why? The reason is very simple – useful files may disappear along with the computer virus. In addition, an overwhelming majority of antivirus tools are not powerful enough to kill all the viruses in a computer. After all, the update rate of virus is much faster than that of antivirus software. What you should do after attack depends on actual situation. Here, we’ll give three solutions on the basis of three situations.
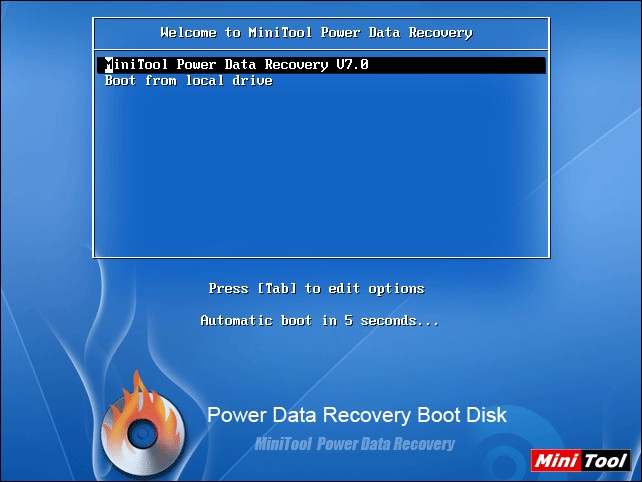
1.If the virus attacks your system boot files so your computer stop running and you’re not able to access it again, you should get MiniTool Power Data Recovery Boot Disk. Burn it into a CD, DVD or USB flash drive. Then, connect it to computer and change the startup settings to make computer starting from this boot disk.
After that, above interface will show and you can click on the first option to continue or just wait to let software move to the next step automatically. In the next step, you will enter main interface of the software, and you can choose either “Damaged Partition Recovery” or “Lost Partition Recovery” to get back lost files.

2.If you fail to access a certain partition after virus invasion, you may see this message – “*:\ is not accessible. The file or directory is corrupted and unreadable”. At this time, you can make sure that this partition has been damaged by virus unfortunately. Sometimes, you may even find the file system of such partition become RAW. In this case, don’t try to format it to make it work normally since that will lead to data recovery failure. To be honest, this is a common problem for hard drive partition as well as thumb drive.
Just connect the thumb drive to a computer which installs MiniTool Power Data Recovery (if the damaged partition is on computer hard drive, please omit this step). Then, launch the software, choose “Damaged Partition Recovery” from main window and carry out following operations under guidance.

3.If a certain partition is lost from hard drive or mobile storage device, users should just make use of the third functional module of Power Data Recovery – “Lost Partition Recovery”. The operating steps are similar to that in situation 2.
There’s one thing that all users should pay attention to: the free edition of Power Data Recovery has a limitation in the total size of data to be recovered. This limitation is 1GB. If you’re going to recover data more than 1GB, you’d better choose other editions instead.
In conclusion, to recover files with software when all files corrupted after virus attack is always the last choice to minimize possible losses. What we should focus on much more is how to prevent virus infection or how to decrease the possibility at least. Since computer viruses have diversified forms and a fast developing speed and are very difficult to cure, every computer user should be highly alert when he needs to download something from internet.
Don’t download any software from unknown or unreliable sites. Don’t open an email, attachment or a link casually. Hope you can keep all the viruses away from your computer or other electronic devices. If you don’t have a clear answer to the question what is corrupted file, you may as well read the relative page carefully.
